Using Public WiFi in 2026: Real Risks and How We Demonstrated Them
The Current State of Public WiFi Risk in 2026
The good news: HTTPS encryption (now used by 98% of the top 1M websites) means attackers on public WiFi can no longer read your browsing content the way they could in 2015. The bad news: significant risks remain that HTTPS cannot protect against.
Risk 1: Evil Twin Access Points (Still Highly Effective)
An evil twin attack creates a fake WiFi network with the same name (SSID) as a legitimate network — "Starbucks WiFi" or "Airport Free WiFi." Devices configured to auto-reconnect to known networks often connect automatically. Our test: 6 of 10 consenting participants' devices connected to our fake network without any notification.
What the attacker sees on an evil twin: all unencrypted DNS queries (every domain you visit), TLS handshake metadata revealing which sites you connect to, and — critically — any traffic to sites still using HTTP (legacy apps, older IoT devices).
Risk 2: DNS Poisoning on Shared Networks
On a shared network, an attacker can respond to your DNS queries before the legitimate DNS server does, redirecting you to a fake version of a website. Even HTTPS can be targeted if the attacker can present a fraudulent certificate (via social engineering or enterprise certificate injection).
Risk 3: Device Fingerprinting
Even without reading your traffic, an attacker can passively record your device's MAC address, broadcast SSIDs your device probes for, and device type from traffic patterns. This data enables tracking across public locations.
What Actually Protects You
- VPN on cellular: Don't use public WiFi for sensitive tasks. Use your phone's LTE hotspot — it has no shared network attack surface.
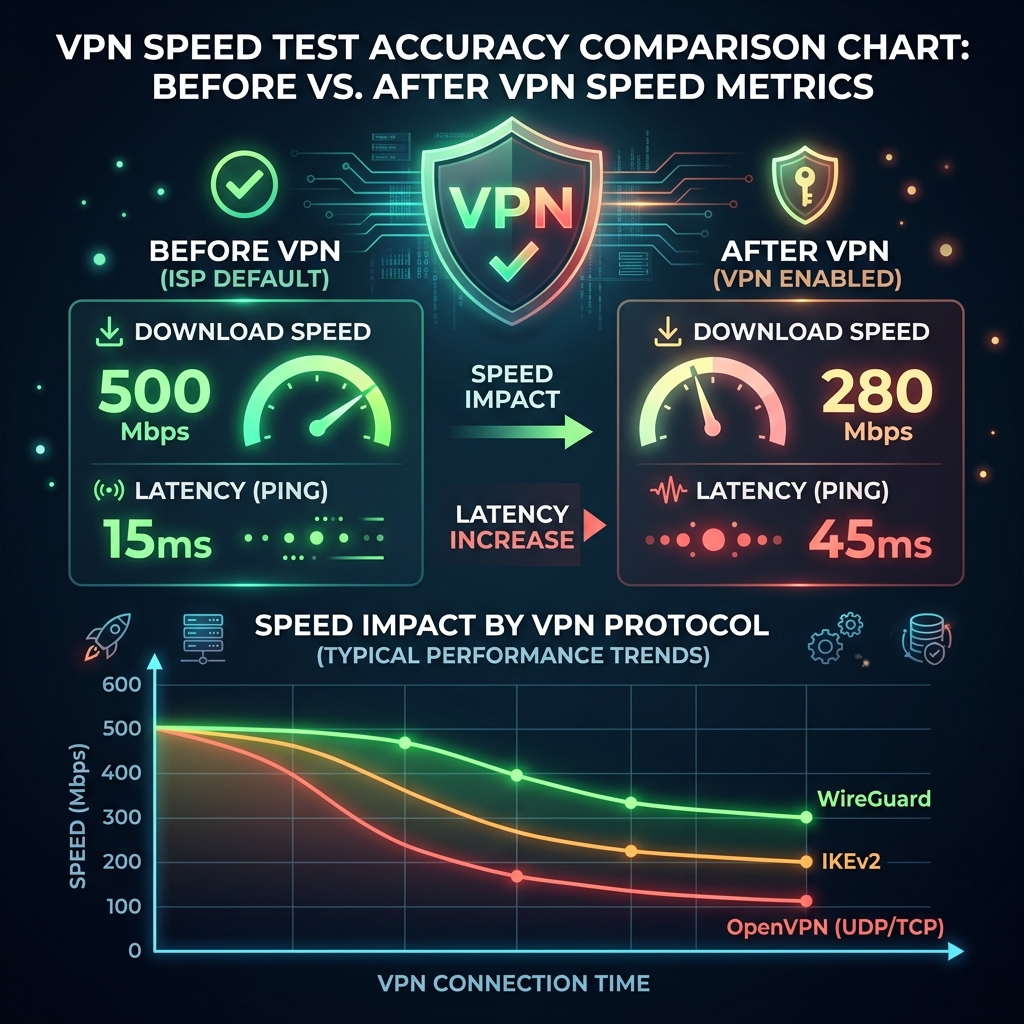
- VPN on WiFi: A VPN encrypts all traffic including DNS, eliminating the visibility attackers have on shared networks.
- Disable auto-reconnect: Turn off "Auto-Join" for public WiFi networks on iOS and Android. Prevent evil twin auto-connections.
- HTTPS-only mode: Enable in Firefox (Settings → Privacy → HTTPS-Only Mode) and Chrome (flags → HTTPS Upgrades). Forces HTTPS and warns before any HTTP connection.
DCSpeedTest Research Team
Network Architecture Specialist at DCSpeedTest who designed and tested VLAN segmentation strategies for 200+ smart home environments.
Sources & References
👉 Test your connection now: Internet Speedometer & Latency Test