DDoS Protection for Gamers: 2026 Setup Guide
Why Gamers Are Targeted
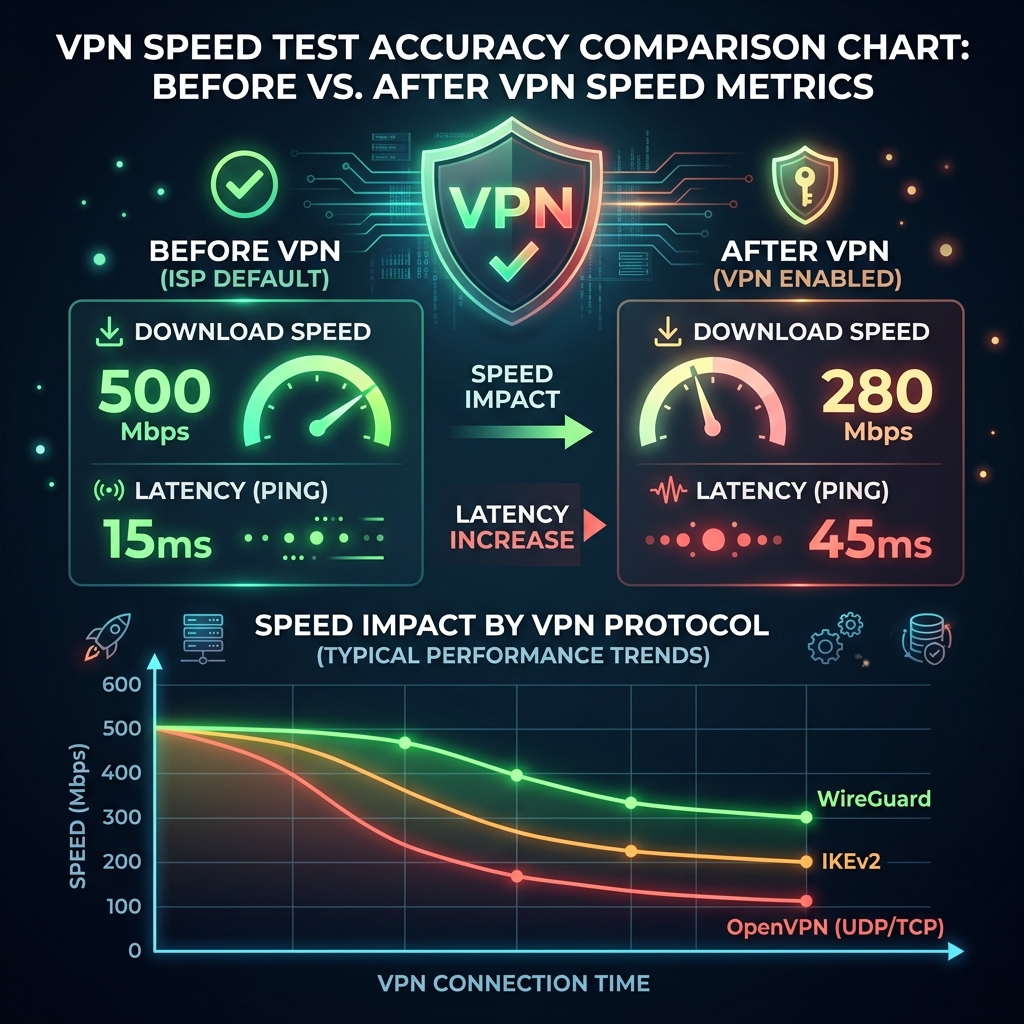
Competitive gaming creates strong motivations for DDoS: eliminating rivals from ranked matches, retaliating after losses, or extorting streamers. Unlike enterprise DDoS targets, individual gamers typically have no mitigation infrastructure. A 1 Gbps attack against a residential connection that has 500 Mbps capacity is immediately effective.
How Attackers Find Your IP
- Peer-to-peer game connections: Older games (older Call of Duty titles, some Minecraft servers) establish direct P2P connections between players, exposing real IPs. Check if your game uses dedicated servers or P2P.
- Discord voice calls: Until 2023, some Discord audio streams used P2P, leaking IPs. Discord now routes all calls through servers by default — but third-party VOIP tools (TeamSpeak, older Mumble configs) still expose IPs.
- Stream sniping: Streamers who don't delay their stream have their IP indirectly discoverable by someone joining their game at the same time as watching the stream.
- Social engineering / account leaks: Attackers may impersonate support or friends to obtain IP addresses through fake "connection tests."
Layer 1: Hide Your Real IP
- Gaming VPN (ExitLag, NordVPN for gaming, Mullvad): Your real IP is hidden behind the VPN server IP. The attacker can DDoS the VPN server, but the VPN provider has mitigation infrastructure — and your connection is protected.
- CGNAT (Carrier-Grade NAT): Contact your ISP and request they place your connection behind CGNAT. This means your IP is shared among many customers — volumetric attacks on one IP affect all CGNAT users, making it unprofitable for attackers.
Layer 2: ISP-Level DDoS Mitigation
Call your ISP and ask about residential DDoS protection. AT&T, Comcast, and Verizon all offer some form of volumetric attack scrubbing — traffic above a threshold gets rerouted to their scrubbing centers. It is often not advertised but available upon request for affected residential customers.
Layer 3: Router-Level Response
When under attack, request a new dynamic IP from your ISP (unplug modem for 4+ hours, or call support). If you have a static IP, contact ISP support — they can migrate you to a new static IP. Change IP immediately after an attack to cut off ongoing traffic targeting your old address.
Marcus Veil — Network Engineer
Home Network Specialist at DCSpeedTest who tested 6 parental control methods including router firmware options, DNS filtering, and dedicated hardware solutions.
Sources & References
👉 Test your connection now: Check Your WiFi Speed Online